How to create secure passwords you will remember
Like many other internet users, I have dozens, perhaps even hundreds of accounts across various websites. Unless there is an option to register via Google or Facebook, the site requires a password from me whenever I create a new account. In most cases, it must be at least 8 characters long, contain at least one number, one capital letter, and a special character. It also needs to be a password that I haven’t used elsewhere before. The question is how to remember all these passwords and still maintain appropriate security.
A simple answer would be to store them in the browser or an add-on/app.
However, there are times when I appreciate remembering the password off the top of my head, for instance when I’m logging in from a new (borrowed) device without having to log in to the browser beforehand. Not to mention that I wouldn’t be able to transfer the passwords stored in some add-ons or apps this way. It is hard to say whether storing your passwords anywhere is secure – once an attacker gains access to that storage, they would get the passwords for all my accounts.
Before I fill my brain so full of passwords that it won’t hold anything else, I can divide the accounts I create passwords for into two categories:
- accounts that I want to be highly secure and/or where I want to log in quickly and easily, and
- accounts where I wouldn’t mind if my password was forgotten or cracked.
For the second category, I can use a browser/add-on/app to store my passwords + an email to receive a password reset request in case of emergency, for which I know the password by heart, but make the actual logging in to it secure.
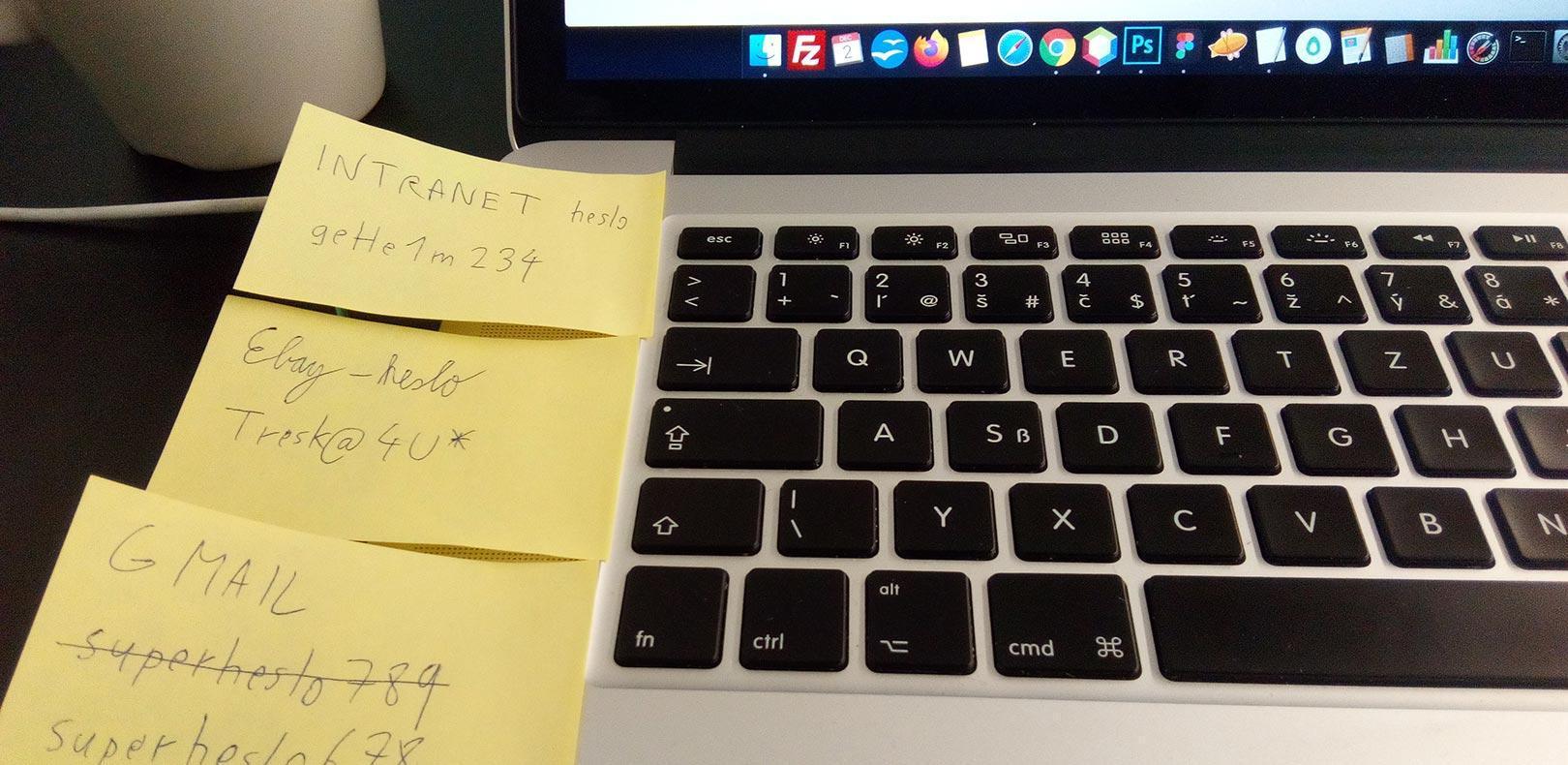
That way I just need to remember a few passwords, but also keep in mind that some accounts (e.g. Google’s G Suite) require me to change my password every few months to a new one that I haven’t used before – despite the fact that it has been criticised as less secure (for instance because people used to write down their passwords on a piece of paper that a visitor could take a picture of), and several, including Microsoft, are moving away from it.
Is the Pa$$w0rd secure?
First of all, the aforementioned criteria of at least one number, one upper-case letter, and a special character is not quite as secure as a longer password without using these criteria.
One of the authors of the 2004 guideline by the US National Institute of Standards and Technology (NIST) admitted to The Wall Street Journal that complex and short passwords had been a mistake.
Based on these criteria, people would create easily cracked passwords in an attempt to create an easy-to-remember one. For instance, a single word in which the letters L and O were replaced by the numbers 1 and 0 and the letters A and S were replaced by the @ and $ characters.
Another problem with short passwords (up to 7 characters) is their potential to be cracked quickly by a brute force attack. Most of the accounts that require a password are protected against this method. However, even then there is a risk that an attacker could discover a security loophole in the service through which they could use a brute force attack, so it is better to choose a password that is also secure against this method.
This method utilises a computer entering all possible permutations of passwords, one by one. For a 5-character long password containing upper- and lower-case letters, numbers, and special characters, that’s only 8 billion permutations.
Allowing for the limitations of data transfer, modern computers (both on the side of the attacker entering the passwords and on the side of the server receiving them) can run an algorithm that attempts a large number of permutations per second. Cracking this password would only take a few hours (possibly minutes).
On the other hand, trying a password twice as long (10 characters), consisting of only lower-case letters (no numbers or special characters), constitutes up to 141 trillion permutations (that’s 17,625 times more), and the brute force method would take considerably longer to succeed.
In more precise figures, if an attacker were to try passwords on their own computer without server data restrictions, a 5-character password comprised of upper- and lower-case letters, numbers, and special characters could be cracked in 8 seconds, while a 10-character password composed of only lower-case letters would take 40 hours. And if 12 characters were used (95 quadrillion permutations), it would take 3 years.
Source: https://web.archive.org/web/20180412051235/http://www.lockdown.co.uk/?pg=combi&s=articles
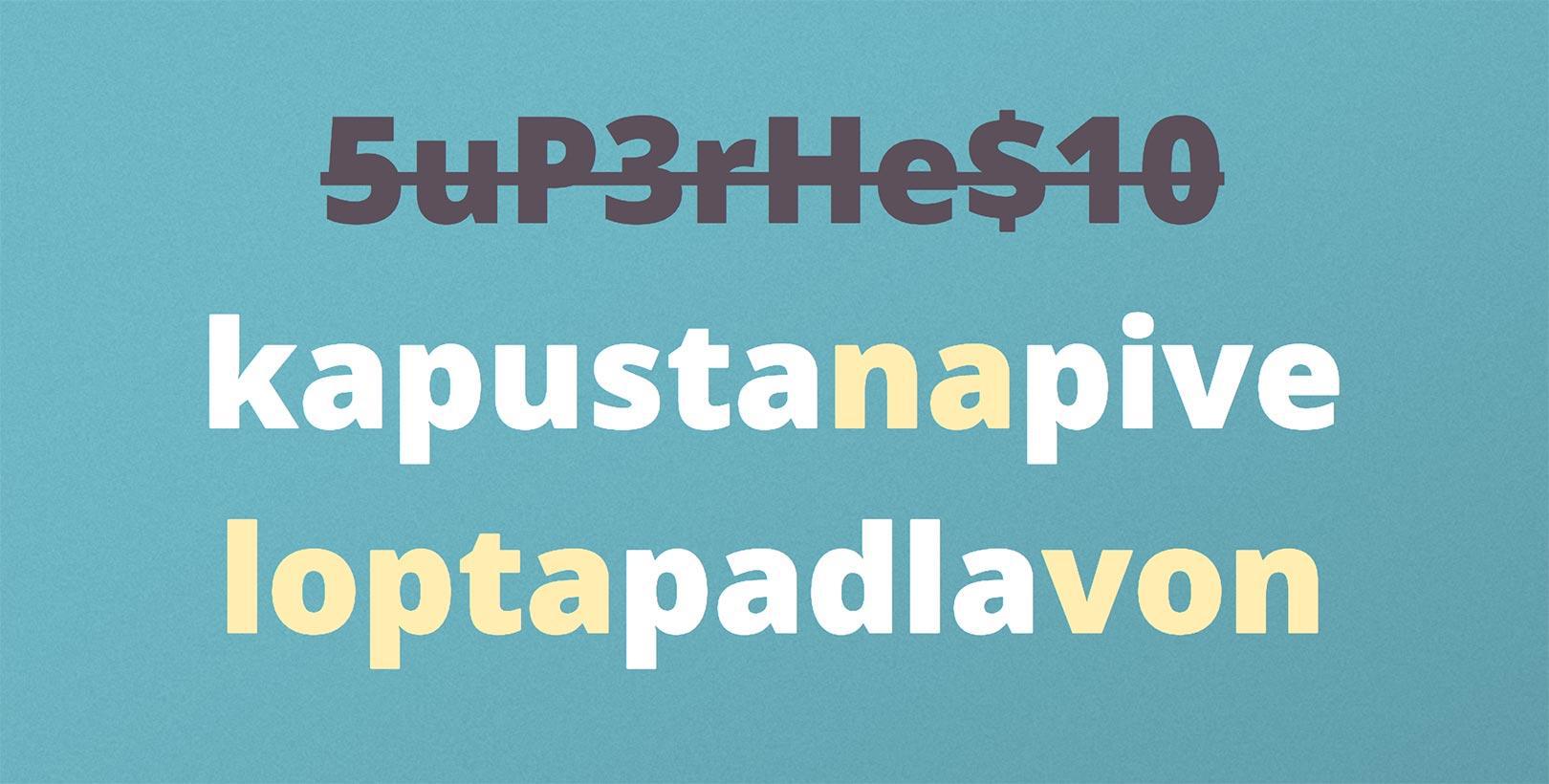
Using 8 characters, which can include upper and lower-case letters, numbers and special characters creates admittedly more than 7 quadrillion combinations (taking upwards of 83 days to crack), but I can certainly remember and type 12 lower-case letters, the equivalent of 2 to 3 words, with more ease and faster than 8 characters including upper-case letters, numbers, and special characters.
How to create a password that is strong and easy to remember?
The author of the original NIST guideline states that it is much safer to create a password consisting of several short, random words. As an example, they gave a password consisting of the words: correct, horse, battery, staple (“correcthorsebatterystaple”). This method of password creation is also in line with the current NIST guidelines 2017. While I agree that such a password is much harder to crack, it is also needlessly long and thus harder to remember in my opinion.
If I use fewer words, I may run into the problem of a potential attacker using a dictionary database to brute-force crack it, trying combinations of all the words one by one (although no attacker would probably attempt it currently, since people have not started using such passwords yet).
The fact is that I continue facing restrictions from services that still require the use of upper-case letters, numbers, and special characters, despite the changing standards.
The easiest way is to use two or three words and supplement them using these criteria. As the number of permutations increases, I don’t necessarily need to pick completely random words. I can keep the same criteria across all the passwords for all my accounts, the only thing I’ll be changing is the words themselves.
For instance, I can create a system where I use the number 7 instead of a space, the first letter is always capitalised, and I use @ as the last character.
Even if someone cracked one of my passwords, e.g. “White7rabbit@”, they wouldn’t be able to identify a system to determine my password in another service, which could be e.g. “Burning7house@”.
You should always avoid words that people most often use for passwords (words like “password”, “top”, “secret”, “lock”, etc.). As a point of interest, this link contains the 500 worst passwords – the ones that people use the most often and are thus the first to be tried by attackers.
I also recommend avoiding the use of diacritics in words because I won’t have to worry later about whether I used them and whether I should type “White7ràbbit@” or “White7rábbit@”.
A less secure, yet still extremely difficult to crack method, is to use the same password for all services and just add a word representing the name of the service. For instance, use “White7@” as the base password and add a name that starts with the same letter as the service, i.e. “White7@frank” for Facebook, “White7@gregor” for Google, “White7@andrea” for Amazon, etc.
Alternatively, these methods can be combined and I will use the base password “White7@” for online shop accounts, while for other services, I will use a different base and choose completely unique passwords for my most frequently used accounts, such as Facebook or Google.
However, I definitely do not recommend using the same exact password with 2 services for which I want the highest security. Not only can my password be leaked from the service I’m logging into, but it can also be intercepted at the time of entering it, unless an encrypted connection (https) was used for instance.
A problem still remains with the services that force me to change my passwords. I just need to find a system once again. It could be simple to end the password with a digit that will gradually increase, for instance. However, if someone finds out my previous passwords, they could easily guess what the current one is.
It might be more secure to use the letters of the alphabet instead of numbers (in sequence) and choose words starting with that initial letter accordingly. This could again be names or animals for easier memorisation. The first password I could use for Google is e.g. “White7@gregorantelope”, the second would be “White7@gregorbear”, the third “White7@gregorcat”…
These are tips for the passwords that you want to secure thoroughly. For accounts where you don’t need maximum security (and which don’t require a special character and number), you may simplify the system to remember the password more easily – for instance, use 3 words (“sausagesandmash”, “ballwasout”…). Even these passwords will be more secure than an 8-character long password containing special characters, upper-case letters, and numbers. I can remember it more easily and type it faster (which I can especially appreciate on my phone).
Of course, everyone prefers a different system to help them remember their passwords easily. My advice is to take the time to devise your own system. That way, you can know all your passwords off the top of your head instead of generating random strings of characters that are impossible to memorise.